News
News
News
Magazine
YouTube
Engineering Fire-Resistant Batteries
Watch Video
Threads
Texas Engineering in the News
-
Can Bitcoin mining really support renewable energy?
The Verge
-
The Sea Creatures That Opened a New Mystery About MH370 Could freaky barnacles do what advanced technology couldn’t — find the missing plane?
New York Magazine
-
Engineering Drinkable Water Cups! From Stanley Tumbler to Navajo Clay Mugs
The Circuit News
More News

First-of-its-Kind Hydrogen Proto-Hub Galvanizes Production of Low-Carbon Hydrogen
The University of Texas at Austin’s Center for Electromechanics, Frontier Energy and GTI Energy today hosted the grand opening of a new hydrogen research and demonstration facility.
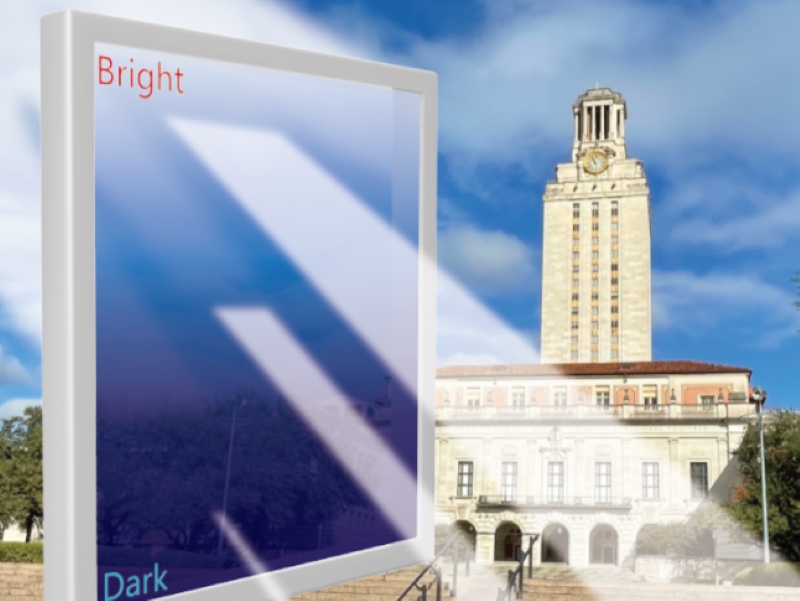
How Potatoes, Corn and Beans Led to Smart Windows Breakthrough
A study from researchers at The University of Texas at Austin aims to reduce the costs of smart windows by creating a new type of electrochromic device and materials.

Texas Engineers Use Erwin Center as Blueprint for Sustainable Demolition
The Frank Erwin Center is coming down to make way for a new UT Austin-MD Anderson Cancer Center joint medical campus, but even in its demise, the former home of Longhorn basketball and many memorable moments in Austin's musical history is serving an important purpose.

3 Cockrell Faculty Members Elected as AAAS Fellows
A trio of Texas Engineers have been elected fellows of the American Association for the Advancement of Science (AAAS), the world’s largest general scientific society.

Cooler Transformers Could Help the Electrical Grid
Following the 2021 winter storm, UT Austin researchers looked inside grid transformers to see if they could make them better.

Karen Willcox Wins 2024 Theodore von Kármán Prize
Karen Willcox, professor of aerospace engineering and engineering mechanics and the director of the Oden Institute for Computational Engineering and Sciences, won the 2024 Theodore von Kármán Prize from the Society of Industrial and Applied Mathematics (SIAM).
Viewpoints

Why Biden’s methane fee is good for U.S. oil and gas
Arvind Ravikumar
Research Associate Professor
Petroleum and Geosystems Engineering










